- This document describes the security content of macOS High Sierra 10.13.2, Security Update 2017-002 Sierra, and Security Update 2017-005 El Capitan. About Apple security updates For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available.
- High Sierra will still work even after security support have stopped. We’ll just have to be vigilant and perform security measures, install an anti-malware, anti-virus software. Though even with.
- In keeping with Apple's release cycle, we anticipate macOS 10.13 High Sierra will no longer receive security updates starting in January 2021. As a result, SCS Computing Facilities (SCSCF) is phasing out software support for all computers running macOS 10.13 High Sierra and will end support on January 31, 2021.
- MacOS Sierra is no longer supported by Apple for Security Updates. UPDATE 6/02/20 – Apple has re-released the 2020-003 Security Update! The new update has a fix for CVE-2020-9859, a Kernel Exploit. “ An application may be able to execute arbitrary code with kernel privilege “.
- Macos Sierra Update To Catalina
- Macos Sierra 10.12.6 Security Update
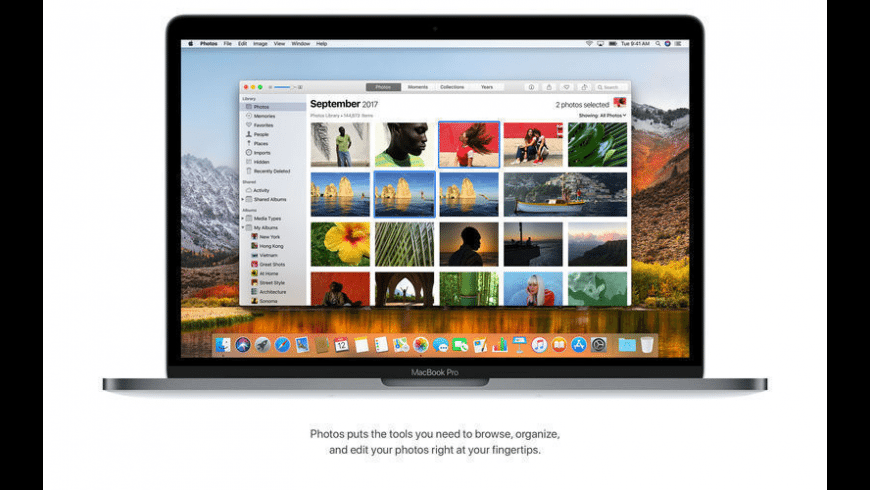
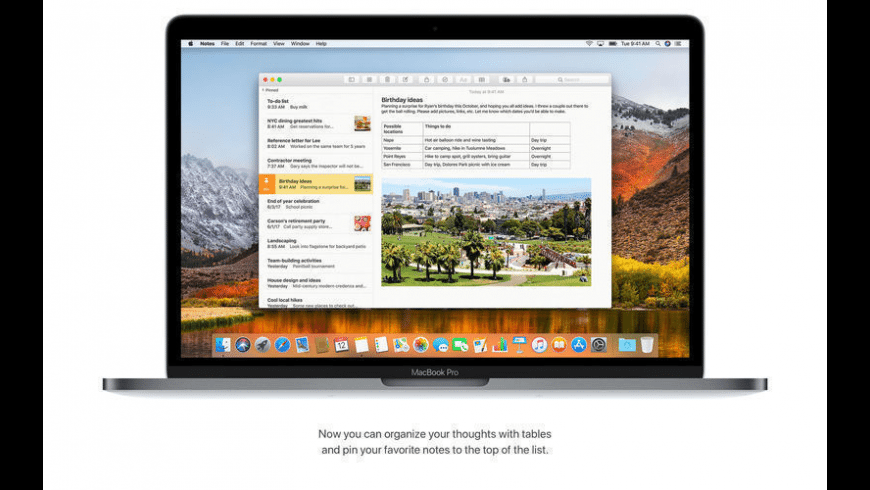
- Macos High Sierra Security Update 2019
- Macos High Sierra Security Update Download
Apple to End macOS 10.13 High Sierra Security Updates This November
About the security content of macOS High Sierra 10.13.3, Security Update 2018-001 Sierra, and Security Update 2018-001 El Capitan About Apple security updates For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available.
From August 2020
Apple will stop all security updates for macOS 10.13 High Sierra in the fall of 2020. That means if you fail to replace your Mac or upgrade your macOS to a newer version by November, you would be putting your data at risk due to less advanced security.
The following computers cannot run macOS 10.14 Mojave or higher and should be replaced by the end of the year:
MacBook Air introduced in 2011 or earlier
MacBook Pro introduced in 2011 or earlier
Mac mini introduced in 2011 or earlier
iMac introduced in 2011 or earlier
Mac Pro introduced mid-2010 or mid-2012
How do I know what Mac and macOS I have?
To see which Mac and macOS you have click on the Apple icon on the top right hand part of the screen and then click “About This Mac” in the drop-down menu.
There it should tell you the kind of Mac you have and which macOS you’re running.
What can I do if I’m still running High Sierra?
If you have a Mac that is too old to update to macOS 10.14 Mojave or newer, please contact us to discuss your options for replacement. If you can update to Mojave or a newer OS, please consult with us first. We will make sure that any software you are currently using will be compatible with a newer OS.
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
For more information about security, see the Apple Product Security page. You can encrypt communications with Apple using the Apple Product Security PGP Key.
Apple security documents reference vulnerabilities by CVE-ID when possible.
macOS High Sierra 10.13.3, Security Update 2018-001 Sierra, and Security Update 2018-001 El Capitan
Released January 23, 2018
Audio
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: Processing a maliciously crafted audio file may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2018-4094: Mingi Cho, Seoyoung Kim, Young-Ho Lee, MinSik Shin and Taekyoung Kwon of the Information Security Lab, Yonsei University
Entry updated November 16, 2018
curl
Available for: macOS High Sierra 10.13.2
Impact: Multiple issues in curl
Description: An integer overflow existed in curl. This issue was addressed with improved bounds checking.
CVE-2017-8816: Alex Nichols
Entry added November 16, 2018
curl
Available for: macOS High Sierra 10.13.2
Impact: Multiple issues in curl
Macos Sierra Update To Catalina
Description: An out-of-bounds read issue existed in the curl. This issue was addressed with improved bounds checking.
CVE-2017-8817: found by OSS-Fuzz
Entry updated November 16, 2018
EFI
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Description: Multiple buffer overflows in kernel in Intel Manageability Engine Firmware 11.0/11.5/11.6/11.7/11.10/11.20 allow attacker with local access to the system to execute arbitrary code.
CVE-2017-5705: Mark Ermolov and Maxim Goryachy from Positive Technologies
Entry added January 30, 2018
EFI
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Description: Multiple privilege escalations in kernel in Intel Manageability Engine Firmware 11.0/11.5/11.6/11.7/11.10/11.20 allow unauthorized process to access privileged content via unspecified vector.
CVE-2017-5708: Mark Ermolov and Maxim Goryachy from Positive Technologies
Entry added January 30, 2018
Macos Sierra 10.12.6 Security Update
IOHIDFamily
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2018-4098: Siguza
Kernel
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read kernel memory (Meltdown)
Description: Systems with microprocessors utilizing speculative execution and indirect branch prediction may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis of the data cache.
CVE-2017-5754: Jann Horn of Google Project Zero; Moritz Lipp of Graz University of Technology; Michael Schwarz of Graz University of Technology; Daniel Gruss of Graz University of Technology; Thomas Prescher of Cyberus Technology GmbH; Werner Haas of Cyberus Technology GmbH; Stefan Mangard of Graz University of Technology; Paul Kocher; Daniel Genkin of University of Pennsylvania and University of Maryland; Yuval Yarom of University of Adelaide and Data61; and Mike Hamburg of Rambus (Cryptography Research Division)
Kernel
Available for: macOS High Sierra 10.13.2
Impact: An application may be able to read restricted memory
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2018-4090: Jann Horn of Google Project Zero
Entry updated November 16, 2018
Kernel
Available for: macOS High Sierra 10.13.2
Impact: An application may be able to read restricted memory
Description: A race condition was addressed with improved locking.
CVE-2018-4092: Stefan Esser of Antid0te UG
Entry updated February 8, 2018, updated November 16, 2018
Kernel
Available for: macOS High Sierra 10.13.2
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved input validation.
CVE-2018-4082: Russ Cox of Google
Entry updated November 16, 2018
Kernel
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A logic issue was addressed with improved validation.
CVE-2018-4097: Resecurity, Inc.
Kernel
Available for: macOS High Sierra 10.13.2
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2018-4093: Jann Horn of Google Project Zero
Kernel
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6, macOS High Sierra 10.13.2
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2018-4189: an anonymous researcher
Entry added May 2, 2018
Kernel
Available for: macOS High Sierra 10.13.2
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2018-4169: an anonymous researcher
Entry added May 2, 2018, updated November 16, 2018
LinkPresentation
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: Processing a maliciously crafted text message may lead to application denial of service
Description: A resource exhaustion issue was addressed with improved input validation.
CVE-2018-4100: Abraham Masri @cheesecakeufo
Entry updated November 16, 2018
QuartzCore
Available for: OS X El Capitan 10.11.6, macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A memory corruption issue existed in the processing of web content. This issue was addressed with improved input validation.
CVE-2018-4085: Ret2 Systems Inc. working with Trend Micro's Zero Day Initiative
Entry updated November 16, 2018
Remote Management
Available for: macOS Sierra 10.12.6
Impact: A remote user may be able to gain root privileges
Description: A permissions issue existed in Remote Management. This issue was addressed through improved permission validation.
CVE-2018-4298: Tim van der Werff of SupCloud
Entry added July 19, 2018
Sandbox
Available for: macOS High Sierra 10.13.2
Impact: A sandboxed process may be able to circumvent sandbox restrictions
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2018-4091: Alex Gaynor of Mozilla
Entry updated November 16, 2018
Security
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: A certificate may have name constraints applied incorrectly
Description: A certificate evaluation issue existed in the handling of name constraints. This issue was addressed with improved trust evaluation of certificates.
CVE-2018-4086: Ian Haken of Netflix
Entry updated November 16, 2018
Security
Available for: macOS High Sierra 10.13.2
Impact: An attacker may be able to bypass administrator authentication without supplying the administrator’s password
Description: A logic error existed in the validation of credentials. This was addressed with improved credential validation.
CVE-2017-13889: Glenn G. Bruckno, P.E. of Automation Engineering, James Barnes, Kevin Manca of Computer Engineering Politecnico di Milano, Rene Malenfant of University of New Brunswick
Entry added June 21, 2018
Touch Bar Support
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved state management.

CVE-2018-4083: Ian Beer of Google Project Zero
Entry added February 9, 2018
Macos High Sierra Security Update 2019
WebKit
Available for: macOS High Sierra 10.13.2
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2018-4088: Jeonghoon Shin of Theori
CVE-2018-4089: Ivan Fratric of Google Project Zero
CVE-2018-4096: found by OSS-Fuzz
WebKit
Available for: macOS High Sierra 10.13.2
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2018-4147: found by OSS-Fuzz
Entry added October 18, 2018
WebKit Page Loading
Available for: macOS High Sierra 10.13.2
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2017-7830: Jun Kokatsu (@shhnjk)
Entry added October 18, 2018
Wi-Fi
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
Macos High Sierra Security Update Download
CVE-2018-4084: Hyung Sup Lee of Minionz, You Chan Lee of Hanyang University
